Those who use Textra and ChompSMS for their messaging needs will soon be treated to new updates today. We’re looking at version 3.1 for the former, and version 7.1 for the latter. These updates will carry with them a feature that’ll make those who’ve heard of the Stagefright vulnerability (read up in case you haven’t, it’s important) take notice: their claim is that “Stagefright Protection” is now built-in, calling it a “rock solid solution.”
So what exactly does this mean? Reading the company’s online knowledgebase turns up the following explanation:
The stagefright exploit can occur when any SMS / MMS app creates the MMS video thumbnail that it shows in the conversation bubble or notification or if a user presses the play button on the video or saves to Gallery. We have provided a solution for ‘StageFright’ in Release 3.1 of Textra out now.
Very Important: In other SMS / MMS apps, turning off auto-retrieve is **NOT** enough as once you tap ‘download’ the exploit becomes active. Additionally you would not get any MMS pics or group messages. Not a good solution.
Sounds good, right? Not exactly.
We take issue with a couple of things in regards to that statement and release. For starters, the whole “Stagefright exploit” thing is a bit misleading. Stagefright on its own is not an exploit. Stagefright is a multimedia library built into the Android framework. That particular library has a vulnerability, which a malicious application (which is not yet known to exist) can use to exploit it. It’s important to make that distinction if for nothing more than to be clear about what, exactly, we’re facing here.
Getting that out of the way, the next thing to note is that it’s unlikely a simple app update can “solve” the Stagefright issue. They can take steps to help better protect users, though, and to Textra and ChompSMS’s credit that’s what we believe is going on here.
From what we can tell, this “Stagefright Protection” feature is a simple “disable automatic MMS downloads” function that exists in nearly every competent messaging app out there, including Hangouts, Android’s built in messenger and other third-party options. The difference with Textra’s feature is a neat new name, and a few warnings about Stagefright before allowing the user to download the video.
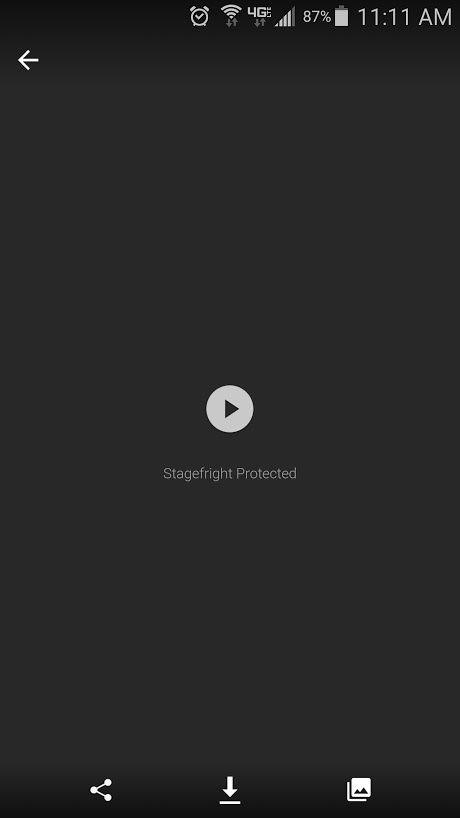
Here’s what happens when you receive an MMS in TextraSMS with Stagefright Protection enabled:
As you can see, the message was not downloaded and the thumbnail hasn’t been resolved, so if this video has an exploit targeting Stagefright then it will not yet be able to execute its code. The message has a nice “Stagefright Protection” label beneath it.
This is what turns up when you hit the Play button on the MMS message: an even bigger box, with an even bigger play button, and an even bigger “Stagefright” label.
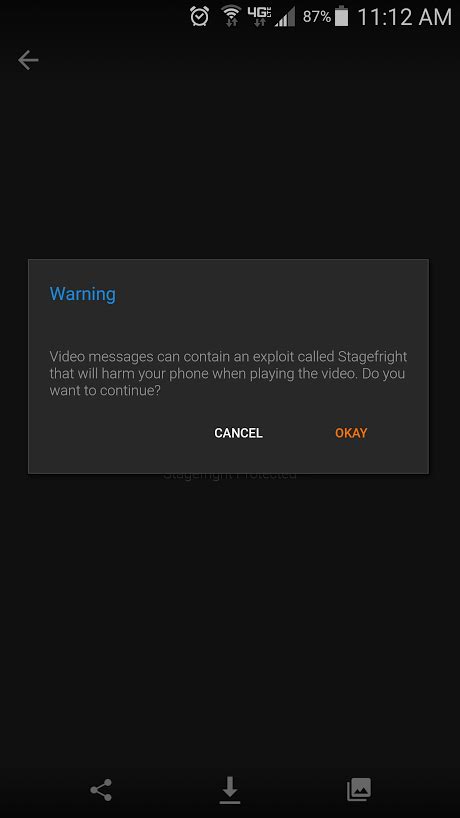
Finally, clicking the Play button one last time will bring up a nice warning message reminding you that downloaded videos may contain an exploit called Stagefright (remember, there is no known exploit, and if there were its name wouldn’t be Stagefright as Stagefright is simply the name of the multimedia library that is vulnerable to being exploited).
Pressing the OKAY button will then bring up whichever video you were going to view, and that’s it. If said video actually did contain an exploit that targets Stagefright then it would, in fact, execute at this moment.
And that’s that. This is as much “protection” as seeing a yield sign on the road. It’s not actually stopping you from going ahead and playing the video, but you should know that there’s a chance (albeit, in this case, a very very small chance) that the video could contain code which could harm your device.
Granted, this is more than other apps are doing against so-called Stagefright exploits at this point. It’s good that they’re being communicative and letting the user know that there’s a potentially dangerous flaw that may put their device at risk. We just wish they didn’t have to do it in a way that looks like little more than a tacky marketing ploy to win a few more downloads.
We’ve reached out to Delicious Inc., who owns both Textra and ChompSMS, for comment and clarification on this feature, and we’ll be sure to report back with a follow-up story once we’ve heard from them.
[Thanks to the folks at AndroidForums.com for bringing it to our attention!]











Comments