Another day, another Android security scare so it seems. The latest comes by way of what researchers are calling the “Fake ID” exploit. The vulnerability — found in all Android devices since 2.1 — allows for malicious applications to bypass normal Android security by faking their secure IDs, giving them access to potentially sensitive data like user credentials, emails, payment history or anything else you’d like to keep away from prying eyes.
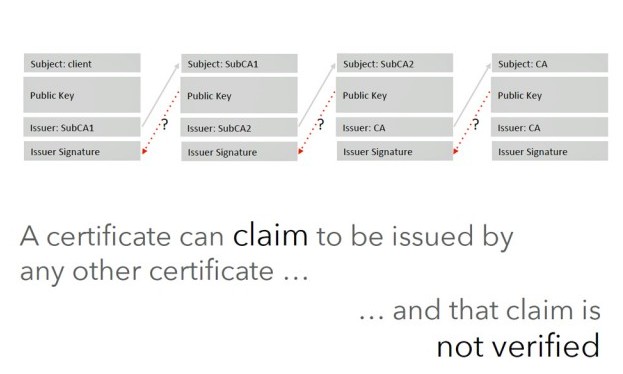
How is this possible? It’s simply because Android fails to verify the validity of an app’s cryptographic signature, something the OS uses when deciding which special privileges to grant an app (like access to NFC or act as a plugin) allowing it to bypass normal Android sandboxing. Apparently KitKat has helped curb some of what this exploit allows, but it’s still left somewhat vulnerable.
Upon hearing the news, Google was quick to respond to the issue and even though there hasn’t been any recorded incidences of the malicious apps actually attacking anyone’s devices, they thanked the folks at Bluebox Security for their findings. The good news? A patch has already been pushed to AOSP and sent to OEMs for them to apply as they deem fit. The bad news? There’s no telling how long something like that can take before it hits your T-Mobile G2X. Here’s the statement Google gave ArsTechnica:
“We appreciate Bluebox responsibly reporting this vulnerability to us; third-party research is one of the ways Android is made stronger for users. After receiving word of this vulnerability, we quickly issued a patch that was distributed to Android partners, as well as to AOSP. Google Play and Verify Apps have also been enhanced to protect users from this issue. At this time, we have scanned all applications submitted to Google Play as well as those Google has reviewed from outside of Google Play, and we have seen no evidence of attempted exploitation of this vulnerability.”
In the meantime, you may want to exercise a little caution when downloading any “special” apps not found on the Google Play Store.










The sad thing is that Blue box reported this to Google 3 months ago, and only after they went public with the exploit did Google acknowledge it and issue a patch. Not what I’d consider a quick response.
I’d like to know how soon Google Play Services were updated to protect from this vulnerability though. That’s the real key here seeing as 93% of all Android devices (Google’s Android) are using the latest version of Play Services, protecting them from this vulnerability.
If Google Play services could block this vulnerability, a patch would not need to be issued. Going off the released information, I don’t think that Play Services is capable of blocking this.
Not everyone uses Google Play Services. AOSP is not the same thing as Google’s Android. For example, Amazon uses AOSP code, but they do not use Google Play Services. Google still has to patch AOSP for those not playing inside their realm.
I’m sorry, but I failed to convey my point properly. I’ll try better.
This flaw was with an underlying issue with the way that Android handles cryptographic signatures and verifying such. It seems that Android verifies at install, and then doesn’t check anymore (gross oversimplification of the issue). This (in theory) allows a rogue app to mimic a previously installed app’s signature.
This change is to Android’s underlying security. Google Play Services’ change was reactive as it scans for the issue in the Play Store and on installed apps. GPS is like a virus scanner in this regard. The fix to AOSP prevents this from even occuring on patched devices.
I hope I’ve made my post more clear.
That’s a very good point, Derek. Most people wouldn’t have considered that.
Didn’t the same thing actually happen to Snapchat several months back?
Excellent choice for the article picture
McLovin. Worst and funniest fake ID ever.
The high point of Rogen’s writing career, of all the mediocres, he is the mediest, to paraphrase…
Damn, I have been using this to bypass the ids so that I can access my work email from my smartphone. ‘Cus Im Lazy.
Knew someone would patch it eventually….
2 years of getting it done ain’t bad.
I’m on Verizon, so I expect to get this update for my S4 in about 2 years.
Please help. got galaxy s5 and have to turn off wi fi before I can receive any calls,texts or emails. This is driving me crazy as I,m eating into my allowance. Please, please advise me what to do do. I am with Virgin media uk and they are blaming Samsung. :(