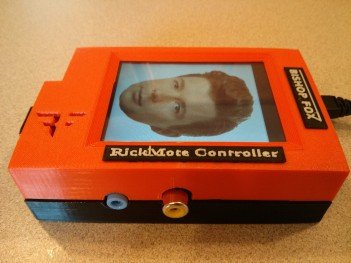
WARNING: Your Chromecast is no longer safe… from hackers with the time and knowledge to build a hacking device out of a Raspberry Pi. As far fetched as that may sound, it is possible. In fact, one man — a security consultant named Den Petro — actually went through the trouble of creating a little proof-of-concept device he calls the “Rickmote.”
The tiny device — built using an affordable Raspberry Pi — takes advantage of an exploit that allows it to easily hack into your Chromecast and play whatever video (or music or pictures) it liked, with no way for you to regain control. Because Rick Astley’s famous music video was the streaming media of choice, that’s how the device found its name.
How it works is the Rickmote floods the Chromecast with de-authenticate packets, a normal function found in the WiFi standard. It’s only because of the unique way the Chromecast handles deauth commands that makes it susceptible to hijacking. When faced with too many deauth commands, Google’s dongle will simply boot into setup mode, making it easy for a very bad person to connect to the dongle and stream whatever they liked.
In fact, the Rickmote doesn’t even need to be connected to your secured WiFi network to hack into the Chromecast, making it all the more threatening (or annoying, rather). Since this is actually how the Chromecast was designed to work, it seems unlikely Google will make an attempt at addressing this newly discovered “exploit” unless they revised the hardware somewhere down the road.
So what are the odds you find your Chromecast hijacked and playing the most exotic adult movies the internet has to offer? Extremely unlikely. First, the prankster would need to be in range of your network — as well as one of their own — in order to stream their own media to your Chromecast. Once they got out of range, the Chromecast would be yours to setup again. For now, we’re sure your Chromecast is (probably) safe.
[Bishop Fox | via Raspberry Pi | TechCrunch]











TL, Dr…i’m really shaking in my petticoats on this one. /s
Pure sensationalism. Not only would they need to be in range they would have to be on my network. … but they can’t, so they can’t do it at all.
Yeah you could be watching something interesting and all of a sudden out of nowhere you get Rickrolled.
There’s nothing so terrible as having someone to hijack your dongle. Oh, wait…
Hijack your dongle. Sounds good
in other words it’s possible to hack into our chromecasts to play whatever we want?
Don’t touch my dongle!
“You have unlocked Rickroll level: Gandalf”
In related news Rick Astleys song was removed from YouTube cause Google got Rickrolled.
They can do a portable hotspot if they really wanted to troll someone heck they don’t even need internet if they use something like this http://www.amazon.com/dp/B00INMB23Q
Hijack your dongle…heh.
So you’re basically saying if they hijack my Chromecast I might get free porn?
Sounds like to much of a pain to give someone free porn.
LOL… he thinks like me. The first thing I did when I set up my Chromecast was to name it “Rickrolling Made Easy” and to troll my unsuspecting wife with the same video.
Reminds me of what I did to annoy my grandpa, when I lived in his home during university years. Back home we had a wired radio signal in every old apartment, so you’d just plug a simple cheap receiver to listen to a few major networks. So whenever me and grandpa had an argument, I’d go to my room, where the second outlet of that wire was located, put a wire pair into that outlet and plug the other end to my vinyl player’s output. Volume up and I flood the wire with my own music. He’d get so pissed off not getting his news broadcasts on time ;) The side effect was that given the output signal was loud enough, I’d flood entire building’s radio network.
Giggity.
I have a feeling it would free gay porn.
Not that there’s anything wrong with that.
Only my wife is allowed to hijack my dongle. lol.
So in other words 99% of us with Chromecasts have nothing to worry about ?
Basically yes