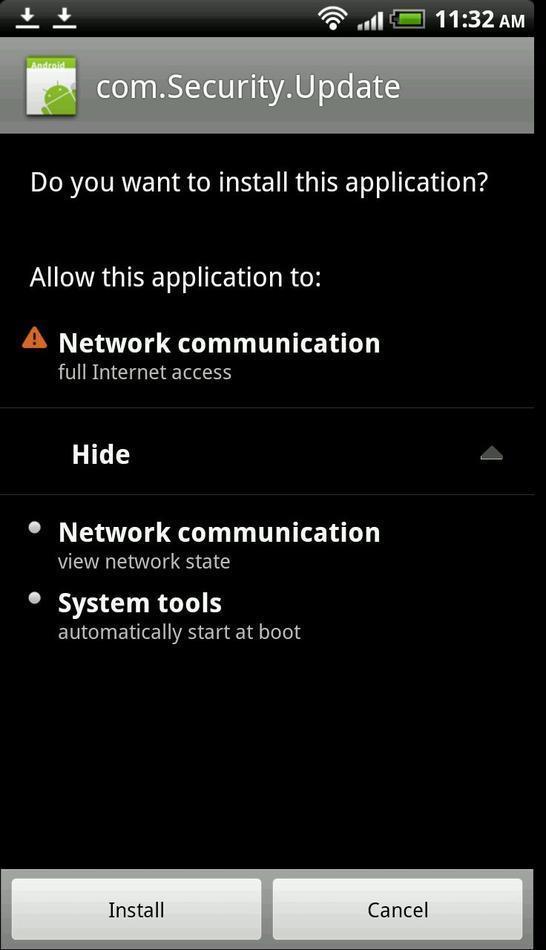
The latest Android malware scare is straight out of Compton. Mobile security firm Lookout reports that Android users have been the victim of “drive-by” attacks that see hacked websites sideloading malicious apps onto their devices. The method of infection, which is most commonly used to target PC users and only recently starting to crop up on mobile devices, uses an embedded iframe to trigger an HTML script that automatically pushes a trojan dubbed NotCompatible. Users are prompted to install the app, which appears as a normal system update.
NotCompatible acts as a TCP relay/proxy and is linked to a command and control server at notcompatibleapp.eu; it could be used to turn an Android device into a proxy for accessing private networks. So far Lookout says the trojan app has not caused “direct harm to a target device.”
Ten sites have been identified as sources for the malware so far, but there could be more. A few steps users can take include disabling the ability to install apps from non-Google Play sources and using common sense when prompted to install anything that wasn’t downloaded from Google’s store.
[via ArsTechnica]










Use common sense?! We’re screwed! :D
Common sense *IS* all that’s required. Unfortunately, it’s not nearly as common as the name would imply.
That’s pretty sneaky, but I would NEVER hit install if the package manager just came out of nowhere trying to install an app. Unfortunately a lot of people with think its just an automatic update or that they caused it somehow.
http://fc08.deviantart.net/fs70/f/2010/157/0/6/Common_Sense__The_Best_AV_by_Spritanium.png
The 2010 version has bugs. Most of them were fixed in the 2011 version, but now they’re back in the new 2012 release.
Wait a minute, I’m not supposed to install every app that prompts me for an install request?
Sorry I created it.
Uh huh, suuuuure. Next you’re going to tell me I shouldn’t download the zip file on the USPS notification I get for a package that I’m not even expecting but seems to be held at a facility at a daily charge of $3.72. Or that there really isn’t some made up pizza chain that is going to deliver $80 worth of pizza to me unless I click their link. Or that there aren’t several rich princes in Nigeria who need my help off shoring their vast wealth. Btw, forward this to ten people you know or you’ll burn in hades with a recent Android phone but no hope of ever seeing ICS… because you’re in hades… and that phone happens to be on a US carrier.
woman at work opened that ups email 2x’s, first time not realizing the reason her machine was infected was because of that email. lol
Yikes! That email is loaded with alarm bells!
Yeah, I am still astonished she did it not only once but twice.
Sent from my Galaxy S II
it only happens if you install apps you don’t know where they came from
Ten porn sites or free music download sites?
Unfortunately with people who install the Amazon App Store on android handsets, you have to enable the ability to install 3rd party apps. This is where most of the common sense goes out the window if a situation like this came up.
Call the apk com.Ice.Cream.Sandwich.update, and the damage rate will be 1000 times higher.
Most users have the option to sideload apps disabled anyway. I dont see this as much of a concern because most users who know to enable the ‘unknown sources’ option have the common sense to prevent a malicious app from forcing itself into the phone.
This may or may not be related but I just got a notification ad for cartoon wars and it just said frreeeedoomm!