Security firm Zimperium has performed an analysis of the way AirDroid communicates with other devices and has discovered the app contains a vulnerability that could allow a malicious third-party to execute code on a targetted device.
The report says that AirDroid itself relies on an insecure communication method in order to send data that authenticates devices to their statistics servers. The requests themselves are encrypted, but the encryption key is hardcoded inside the application, so the attacker can acquire that key and execute a man in the middle attack on devices running AirDroid.
Here’s a quick video that demonstrates the flaw in the code.
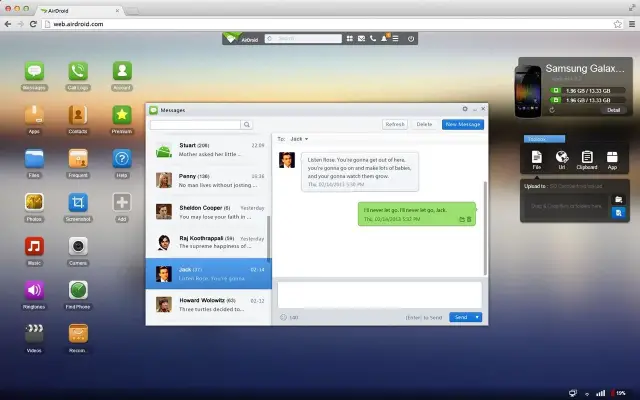
With the device’s authentication information, the attacker can now impersonate the victim’s device to perform any HTTP or HTTPS requests. While that can allow the hacker to send a request for the victim’s email and password hash to the AirDroid API, by setting up a transparent proxy and modifying the response for a certain line of code, attackers could execute custom code on the device.
With that modification in place, the AirDroid app will notify the user that there’s an update available to install, it will download the malicious .apk file the attacker specified, and prompt the user to install it on their device. This could have severe implications for anyone that uses AirDroid over an insecure WiFi network.
Zimperium notes that AirDroid does rely on secure HTTP API endpoints, but it found other insecure channels are used to perform specific functions in the app. What’s worse, is the company notified AirDroid about these vulnerabilities back in May, but the developers have yet to do anything about them. The full timeline of communication between Zimperium and the AirDroid developers shows they’ve had almost six months to address this problem, yet they haven’t.











Comments