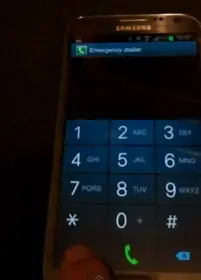
It appears Samsung’s phones are a tad insecure. A new flaw has been uncovered by a user that puts the home-screen of a user’s locked device at risk. In case you don’t know, the pattern and password unlock screens on Samsung phones offer access to the emergency dialer. From there, you can access the user’s ICE contact list.
Pressing the home or back button should normally take you back to the lock-screen, but Samsung’s latest phones — such as the Galaxy S3 and Galaxy Note II — incorrectly display the home-screen for a brief second at this point. The home-screen is show just long enough for you to see which apps and widgets are on that default home-screen, and you can even launch an app if you’re quick enough. The lock-screen will come up even if you do manage to get the app open, but there’s still reason to be worried here:
- If you have any sensitive info on your home-screen, like something a widget might show, peeping eyes could see all of that in one or two glances.
- If you have a direct dial widget for a contact on your home-screen the culprit could dial people you don’t want them to.
It’s not too alarming in the grand scheme of things, but we imagine it’s something Samsung won’t want to take lightly. The fix would appear to be rather simple, though, so we’ll see what they say in response to the flaw and inquire about any potential updates to address it in the near future. Watch a quick video of the flaw in action above.
[via PhoneArena thanks Joel!]









And THIS is why stock Android trumps all.
Disclaimer: No, I’m not saying that stock Android is “perfect”, just that things like this don’t happen on stock because some 3rd party isn’t screwing around with the code. This is what, the 3rd security flaw in the past year (365 days) for Samsung?
Don’t forget about the android 2.0 flaw that even if the screen was locked if you got a call all someone had to do was hit the back button and bypass any security the phone had on it. Thankfully that was fixed with 2.0.1
I’m pretty sure that was fixed relatively quickly, and just about every manufacturer that updated to 2.0 updated to Android 2.1 at least. There’s no telling when (or if) Samsung will get around this admittedly minor bug, let alone when/if the carriers (here in the US anyway) will get around to “testing” and approving the update.
From what I remember the only phone to have 2.0 was the og Droid and I believe it was on 2.0 for at least two months so ya it was fixed relatively quick especially for Verizon standards.
You are correct
No android device besides the droid had Android 2.0 if Im not mistaken… So it was a controlled situation.
But weren’t some of those security flaws based on the hardware and not the software? I think we need to compare apples to apples. Be fair with your arguments and don’t be misleading.
If there were 3 different software related, then OK.
But the Exynos exploit was fixed with a simple software update. No recalls issued. No return program. If it truly had been a hardware problem, either of those would have been necessary.
Hmm… That is true. But a part of me just feels like that isn’t really “TouchWiz”.
But wasn’t the exploit gone on AOSP ROMs? So I guess that would make it TouchWiz related. I’m guessing a back door through TouchWiz. Hmm… I see…
Wow!! That wasn’t brief. That was like an entire second. I could send a text in that time. I was expecting something shorter. That’s way to dangerous.
Another reason I don’t even deal with screen locking. I just use apps to lock my other apps. SmartApp Protector has a function where when you open the app it tells you it forced closed. You have to hold the “OK” button to go to the password area.
+1 for SmartApp Protector. I’ve tried them all and this one by far trumps the rest. It even has some “extra” features that I like such as the ability to add apps to a section to make it so that those apps either stay in landscape or portrait mode. I also like the ability to disable the SmartApp Protector when I am on certain wifi’s.
Oh my gosh!! Do not get me started. I love how it randomizes the PIN number. That is GENIUS!! You have no idea!! I had a friend that was trying to guess my PIN from looking and guess who couldn’t get the PIN right? =.D
Not a big deal, guys
Or just don’t be stupid and lose your phone.
Please take this post down due to a virus being triggered if you try or have accidentally pressed the keys.
At least it’s not like where someone could bypass the lock screen entirely on an iPhone.
I tried to access the homescreen apps, and they are inaccessible. This “security flaw” has been blown out of proportion!
We were able to recreate the crack in the ICE on a Samsung Galaxy S III on video. See it on http://youtu.be/qCBNLTNmcA4